Network penetration testing can play a vital role in keeping your business well-protected against cyber threats. There are several reasons to consider a pentest, keep reading to find out why many organizations choose Cybriant for their penetration testing services.
It’s important to consider an outside organization to routinely conduct network penetration tests, you’ll be able to ensure that your company is always safe from unknown vulnerabilities.
What is Network Penetration Testing?
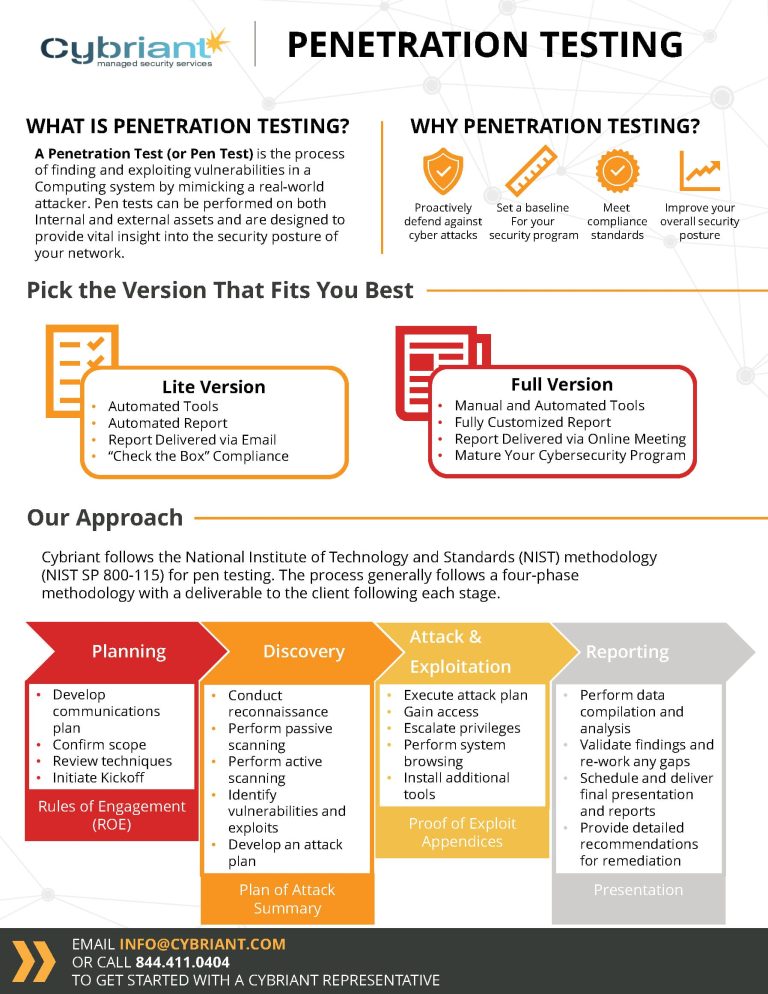
Penetration Tests, often referred to as ‘pen tests’ are necessary for organizations that have a compliance need, that has a concern about a specific system, or are within the monitoring phase of an overarching security program. With Cybriant’s Pen Test, a professional hacker attempts to exploit a technical vulnerability to gain unauthorized access to specified systems. Penetration Tests are commonly misunderstood.
We will attempt to classify our various offerings:
Vulnerability Scan
When a company wants to understand any misconfiguration or known vulnerabilities that may exist in their infrastructure. It is highly recommended that a vulnerability scan be performed before any penetration test. If a penetration tester exposes a known vulnerability during a test that could have been remediated as a result of a vulnerability scan, the customer has wasted their money.
Standard Network Penetration Test
Identifies the actual exploitable vulnerabilities within the attack profile of a customer’s environment. Cybriant’s hackers will test for and verify the authenticity of a possible exploit. Each actual exploit will be cataloged, and a remediation recommendation will be presented. This is primarily for customers who are attempting to satisfy contractual, regulatory, or industry requirements.
Advanced Network Penetration Test
When most people think ‘hacker’ they are thinking of Cybriant’s Advanced Network Pen Test.Cybriant’s professional hackers will attempt to gain access to a customer’s environment. Once access is gained the hacker will depending on customer preferences, reach further into the environment to expose the maximum amount of sensitive data as possible.
Cybercriminals are constantly developing new ways to access networks, but a network penetration testing service provider like Cybriant can help your business remain proactive against these evolving threats.
Here are the top seven reasons why you should consider a network penetration test for your business.
#1 Identify Areas of Vulnerability
One of the main reasons for network penetration testing is that it can help identify potential areas of vulnerability. A vulnerability assessment will evaluate your entire business network to look for any areas that may be susceptible to a data breach or a cyber attack. An IT service provider can also simulate various types of cyberattacks to immediately find any areas of concern that need to be fixed as soon as possible.
#2 Reduces the Risk of a Cyber Attack
Taking the time to perform a network penetration test can play a vital role in limiting the chance of a successful cyber attack against your business. Always staying proactive is essential in looking for ways to improve and avoid becoming complacent. You will have the peace of mind to know that your company is always well-protected by an IT service provider that performs network penetration tests regularly.
#3 Saves You Money in the Long-Term
Business owners are always looking at ways to save money while still keeping their company well-protected against cyber attacks. Performing a network vulnerability test is much cheaper in the long run compared to being the next victim of a data breach or a cyber attack. Making cybersecurity a top priority for your company will help your business stay one step ahead of cybercriminals while helping you avoid the high costs of these malicious attacks.
#4 Maintain Business Continuity
A business continuity plan is critical in helping your company bounce back from any situation while keeping downtime to a minimum. Scheduling a network penetration test is essential to ensure that your network can handle a wide range of threats. An IT service provider will always look at ways to improve your business continuity plan and is never satisfied with the status quo.
#5 Follow Industry Regulations
Many organizations must follow strict regulations for their particular industry. Failure to maintain compliance can lead to significant fines or even the closure of an entire company. Penetration testing can play a crucial role in helping your business maintain regulations for your industry by maximizing cybersecurity to prevent a costly data breach.
Most regulatory acts require affected companies to implement procedures to regularly test and affirm security control effectiveness. This includes regulations such as PCI-DSS, HIPAA, GLBA, and others that impact industry verticals like Retail, Healthcare, Financial Services, Government, and Education. A network test by Cybriant ensures third-party impartiality and regulatory rigor.
#6. Supply Chain Framework and Compliance
Many clients have contractual requests based on their framework. Cybriant’s services are aligned with the NIST Cybersecurity Framework.
Beginning in the fall of 2020, Cybersecurity Maturity Model Certification or CMMC compliancewill be a prerequisite for all new contracts including prime and subcontractor for the Department of Defense. Any contractor storing or transmitting controlled unclassified information (CUI) will need to achieve Level 3 compliance.
The Department of Defense has defined 5 levels of CMMC compliance, each with a set of supporting practices and processes. To meet a specific level, each contractor must meet the practices and processes within that level and below. Learn more about CMMC here.
#7. Cyber Risk Management
A penetration test is the final step in monitoring and assessing the effectiveness of a security program. All frameworks require the testing of security controls and the most common method is a penetration test.
Why Should You Perform a Penetration Test on Your Network?
Consider the following reasons that many of Cybriant’s clients have used our network penetration testing services. If your clients or 3rd party vendors are asking for an external penetration test, these are the reasons it may make sense for your organization:
- Meet regulatory and other compliance mandates
- Value add differentiator to represent a responsible stance while marketing
- Major changes occurred in the environment
- Satisfy the contractual requirement
- Ease customer’s minds
- Critical control in all frameworks, regulatory and other
- Understand the threat to the Environment
- Ensure major changes have not exposed new vulnerabilities
- Identifying higher-risk vulnerabilities that result from a combination of lower-risk vulnerabilities exploited in a sequence
- Identifying vulnerabilities that may be difficult or impossible to detect with automated network or application vulnerability scanning software
- Assessing the magnitude of potential business and operational impacts of successful attacks
- Testing the ability of network defenders to successfully detect and respond to the attacks
- Providing evidence to support increased investments in security personnel and technology to C-level management, investors, and customers
- Meeting compliance (for example The Payment Card Industry Data Security Standard (PCI DSS) requires both annual and ongoing penetration testing
- Post security incidents, an organization needs to determine the vectors that were used to gain access to a compromised system (or entire network). Combined with forensic analysis, a penetration test is often used to re-create the attack chain, or else to validate that new security controls put in place will thwart a similar attack in the future.
- Determining the feasibility of a set of attack vector
In Conclusion
Network penetration testing is critical in maximizing uptime for your business while also protecting the reputation of your company. These vulnerability assessments can identify potential areas of weakness within your organization while also greatly reducing the risks of a cyber attack. Over time, these vulnerability assessments can play a key role in keeping your business well-protected and save you plenty of money in the long term.
Learn about all risk assessments available through Cybriant here.



