Here are the top 4 SIEM use cases for managed SIEM. Many organizations are outsourcing to third-party vendors for faster and better cyber threat detection, and here’s why you should consider it as well.
Given the different challenges facing security departments, security monitoring is vital. Security professionals now feel the deck is stacked against them as cybercriminals continue to attack. Many organizations are outsourcing to third-party vendors for faster and better detection.
 In this article, we want to tackle the most important reasons companies outsource the management of their SIEM to professional security service vendors. When it comes to a strong security program, we believe security monitoring is vital because it is the fastest way to detect anything that can compromise an organization’s systems. This means it is vital to make security monitoring the fundamental and core aspect of any security program.
In this article, we want to tackle the most important reasons companies outsource the management of their SIEM to professional security service vendors. When it comes to a strong security program, we believe security monitoring is vital because it is the fastest way to detect anything that can compromise an organization’s systems. This means it is vital to make security monitoring the fundamental and core aspect of any security program.
Security Monitoring is the #1 Security Service to Outsource
According to this recent Forbes article, security monitoring is the top, most logical security function to outsource to a cybersecurity solutions firm. The article states:
Many organizations lack the budget or bandwidth to set up their security operations center to handle comprehensive monitoring and alerting services. Even large organizations with security teams in the double digits are often tackling other high-priority staffing and transformation projects that put dedicated security monitoring on the back burner.
Fortunately, security monitoring services are one of the commonly provided services by a managed security services provider (MSSP). There is an MSSP for just about every size and budget, but you get what you pay for. The onus falls on you as the customer to define what you need and to hold your provider accountable.
The other security services mentioned that make sense to outsource are incident response, security testing, assessments, and training – Cybriant can help with all of those as well.
Consider the Cost of Building a SOC Internally
 Many organizations set out on a course to build a security operations center or SOC internally. This makes sense for many companies. For most other companies the cost, resources, and other variables are entirely too high to consider building a SOC themselves.
Many organizations set out on a course to build a security operations center or SOC internally. This makes sense for many companies. For most other companies the cost, resources, and other variables are entirely too high to consider building a SOC themselves.
We have gathered all the data, crunched the numbers, and made the comparison charts in this easy-to-read ebook: https://www.cybriant.com/insource-vs-outsource/ Take a look and let us know your thoughts. Do these costs compare to what you were thinking?
SIEM Use Cases for Managed SIEM with Security Monitoring
A SIEM is a complex tool that requires expertise to implement and maintain. To be effective, a SIEM must be constantly updated and customized because external threats and internal environments are constantly changing. It requires experienced security engineering to tune the SIEM to minimize false positive alerts and maximize the efficient detection of real breaches or malicious behavior.
Let’s look at top SIEM use cases that make security monitoring vital for an organization.
#1. Access to Extensive Cybersecurity Knowledge
Your organization can’t just throw people at security monitoring; you need the right people there. The right people are those with expertise in triaging alerts, closing complex problems, and understanding when they should alarm the incident response team. So if your organization has no sufficient internal expertise, you need a managed security monitoring organization that can handle the resourcing for you.
75% of organizations lack skilled cybersecurity experts. There are many training programs in colleges and universities, but there is still an experience gap. By outsourcing to a cybersecurity services firm, you automatically have a deeper bench of resources. You’ll also have access to security best practices, faster mean time to value, lower operational and labor costs, and improved security functions.
#2. Compliance Requirements
Virtually every regulatory mandate requires some form of log management to maintain an audit trail of activity. Ticketing and alerting capabilities also satisfy routine log data review requirements. Simply having a SIEM doesn’t mean it is effective, which is the point of the compliance requirement. Many companies prefer to outsource the management of the SIEM so it is used effectively.
Companies often think that purchasing a SIEM technology and managing it internally will work for them and help them remain compliant. Unfortunately, SIEMs are complex to install and even more complex to manage. Once a SIEM is installed and connected to every device on your network, the flood of events and alerts is more than any one person can handle. Fine-tuning your SIEM will be key, and that is something that our experts can handle for you.
#3. Advanced persistent threats (APTs)
New attack vectors and vulnerabilities are discovered every day. Your organization likely has firewalls, IDS/IPS, and AV solutions installed that look for malicious activity at various points within the IT infrastructure, from the perimeter to endpoints. However, many of these solutions are not equipped to detect zero-day attacks and advanced persistent threats.
An APT is a very complex cyber attack that will invade traditional, signature-based security tools and then hang around in an organization’s environment undetected. Advanced persistent threats can go undetected for months or more; during that time, attackers become intimately familiar with an organization’s network, its security controls, and the location of its sensitive data. APTs typically result in data theft. When you have a security expert watching for APTs around the clock, we can stop it before it causes any issues.
#4. Around-the-clock monitoring
If you want 24/7 security monitoring, you will need more staffing to carry out the job, but managed services already have employees monitoring their security monitoring platform 24/7. That is why managed service is the better option when it comes to round-the-clock monitoring. Check out our document Insource vs. Outsource, cost comparison for building a 24/7 security operations center.
By reviewing your security and event logs around the clock, you’ll be able to reduce your MTTD (mean time to detection). The average MTTD, according to the 2017 Ponemon Cost of Data Breach Study, for a survey of 491 companies was 191 days with a range of 24 to 546 days. Imagine the potential damage that could be done if a breach wasn’t detected for 546 days. By reducing your MTTD, you’ll also reduce your MTTR (mean time to respond). The MTTR in the Ponemon Cost of Data Breaches report found that the average for organizations was 66 days with a range of 10 to 164 days.
SIEM use cases where managed security monitoring is commonly used:
- Advanced threat detection
- Device monitoring/alerting
- Compliance reporting
- And much more
No matter the size of your organization, you need to protect your data. And failure to protect your data puts the company at risk of financial issues, loss of goodwill, and legal liability.
The immediate benefits of outsourcing the management of your SIEM include:
- Malicious activity will be identified and thwarted
- Satisfy compliance requirements and reduce the expense
- Awareness of any evolving cyber threats that may hit your organization
- Improved use of SIEM technology investment
- Dedicated security professionals review security logs and alerts in real-time
- Security expenses are moved from capital to operational
That leaves only one question – WHY WAIT? Our team can have your organization onboarded in days so you can get started ASAP. Go here for more information and to speak to an expert.
Cybriant has worked with many clients to install and monitor their SIEM. Take a look at these specific managed SIEM use cases: https://www.g2.com/products/cybriant/references/cybriant
How Does a SIEM Work?
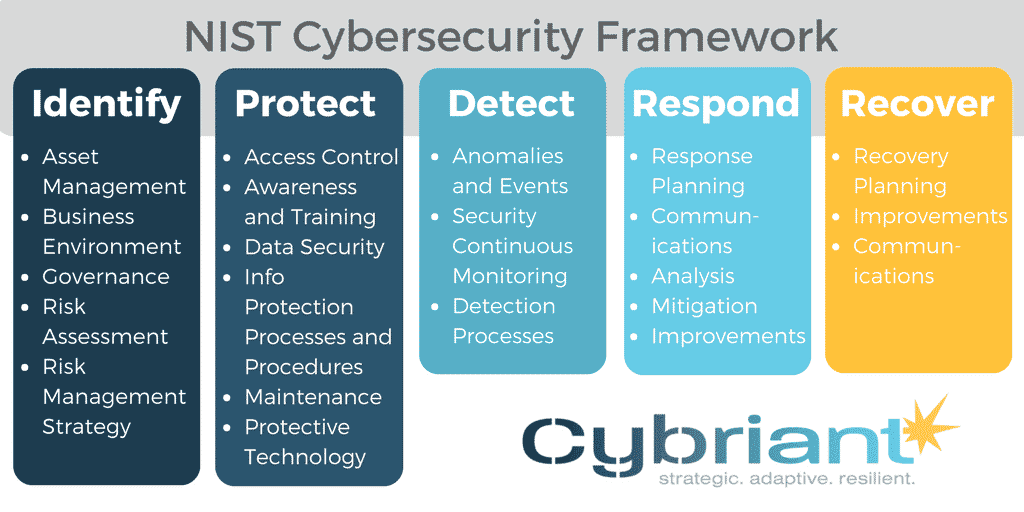
SIEM provides two main capabilities to an Incident Response team:
- Reporting and forensics about security incidents
- Alerts based on analytics that matches a certain rule set, indicating a security issue
At its core, SIEM is a data aggregator, search, and reporting system. SIEM collects enormous amounts of data from your complete networked environment, consolidates it, and makes that data human-accessible. With the data classified and laid out at your fingertips, you can study data security breaches with as much detail as needed. A sample of Cybriant’s managed SIEM use cases can be seen at https://cybriant.com/client-use-cases/
However, experts say enterprise demand for greater security measures has driven more of the SIEM market in recent years. This is why Managed SIEM has gained popularity. Many IT departments are unable to spend the time necessary to draw the data out of a SIEM that will allow them to properly detect cyber threats.
Read more from our article, “How Does a SIEM Work?”
What is the Difference Between SIEM and a SOC?
A SOC – Security Operations Center – is a monitoring center. A SOC is typically comprised of skilled and knowledgeable security analysts that will examine the data coming in from your SIEM and determine if any critical or unusual is happening.
A SOC should have a SIEM to help pull together all the logs and build correlation rules around them.
Many organizations purchase a SIEM and use in-house resources that may not be prepared to handle all the data that comes along with a SIEM.
Based on a recent study on the State of the SOC, security practitioners from enterprise organizations are overwhelmed by the sheer volume of alerts and investigations that require their attention. The results of the study indicate:
- 60% of Security Operations Center analysts can only handle between 7-8 incident investigations per day. — Fidelis Cybersecurity, 2018
- Only 17% of organizations have a dedicated threat-hunting team. — Fidelis Cybersecurity, 2018
Alert fatigue syndrome is a real issue, one of the many bad habits of cybersecurity professionals, and one that they must break to protect their organization. This syndrome means that security analysts may not respond to the security alerts because they are flooded with so many.
Read more about the difference between a SIEM and a SOC.
Next-Gen SIEM
Should you consider a next-gen SIEM?
a Next-Gen SIEM – will ingest both log and flow data – it uses threat models to determine the threats rather than a human brain.
These are complicated models that can detect and match threat behaviors to a particular type of threat such as a DDoS attack vs. a brute force attack, malware infection, APTs loss of credentials, or insider attack. It will leverage but not rely on the proper use of Machine Learning to pick out behaviors that are not normal for the device, application, or user, and correlate these events with other rule triggers that can be correlated into a threat model- once a match is found an alert is built that continues to aggregate individual threat behaviors under the Single Line Alert on the UI – this is vs. 100s to 1000s of lines generated by a SIEM beforehand filtering. Better yet this one line tells you the type of threat and the devices and/or users involved and what to do about it.
The best Next-Gen SIEMs will be architected to detect the threats within minutes of becoming active. Stopping Brute force attacks, compromised credentials, and insider threats before critical data is accessed. SIEMs can’t promise this.
Read more about Traditional SIEM vs. Next-Gen SIEM.
Convince Your Boss You Need These Managed IT Security Services



 In this article, we want to tackle the most important reasons companies outsource the management of their SIEM to
In this article, we want to tackle the most important reasons companies outsource the management of their SIEM to  Many organizations set out on a course to build a security operations center or
Many organizations set out on a course to build a security operations center or