The CEO’s Guide to Managed SOC Services
As the CEO, consider Managed SOC Services to protect your organization. The security of your organization is only as strong as the team, regulations, tools, and services you approve.
What are Managed SOC Services?
Cybersecurity needs vary from organization to organization and are implemented per structural cybersecurity priorities and risk tolerance. Most managed SOC services will manage an incident from detection to remediation; others will focus on supporting and coordinating incident responders and handling incident response communication — e.g., status updates and third-party communication.”
Managed SOC services provide 24/7 proactive security monitoring, vulnerability management, and incident response and remediation. This is especially attractive for businesses that are attacked frequently but do not have the resources of large enterprises.
With the flexible commercial models and deployment options, Managed SOC Services are a cost-effective way for organizations to leverage all the benefits of a SOC without incurring the significant overheads and outlay associated with building and deploying their in-house security center.
The suite of Managed SOC services delivers information security monitoring, incident response, and vulnerability management services that are essential to counter the sophisticated threats of today.
When you outsource the management of a SOC to an MSSP like Cybriant, your organization can quickly improve its cyber security defense without spending exorbitantly on additional infrastructure or keeping a large team of expensive security experts.
How to Meet the Guidelines for the NIST Cybersecurity Framework
Continuous Monitoring with Managed SOC Services
An outsourced team of security experts provides 24/7 continuous monitoring of your environment. This team investigates all incidents that appear to be suspicious and takes immediate remedial action if malicious activity is detected.
24×7 security monitoring utilizing leading Security Information and Event
- Management Systems (SIEM).
- Monitoring of firewall, IDS, anti-virus and operating system logs, and any other sources of security events.
- Going beyond the SIEM and other deployed technology and actively searching for breaches (Premium Service).
- Threat detection and rapid incident remediation (Premium Service).
Threat Intelligence
Security analysts and researchers augment third-party intelligence feeds with threat information generated internally. Additionally, they filter data to highlight specific threats relevant to Managed SOC services customers and their business interests. Threat intelligence plays a critical role in enhancing the detection capability of outsourced cybersecurity monitoring.
Incident Response & Forensics of Managed SOC services
Upon detecting a breach, a member of the Managed SOC Services team will launch incident remediation measures in close coordination with the customer’s IT, team, working to contain the threat whilst ensuring minimal disruption to business activity. This is followed by a thorough incident response and forensic analysis exercise to determine the root cause, eradicate the breach and improve defenses to prevent occurrences of similar breaches in the future.
Here are 3 Benefits of an Incident Response Plan
When you work with a Managed Detection & Remediation team like Cybriant, you can control a breach and remediate it as needed.
Vulnerability Management
An outsourced Managed SOC services team detects vulnerabilities in your IT infrastructure using cutting-edge technology. This team will remediate vulnerabilities to minimize their risk exposure.
- Continuous vulnerability assessment.
- Vulnerability tracking & prioritization.
- Vulnerability remediation.
Ongoing Improvement of Security Posture
Acts as advisor and helps you continuously improve security posture by helping the company define better policies and processes.
Compliance with Applicable Security Standards and Regulations
By working with an MSSP, they can help you achieve compliance with standards and regulations such as HIPAA and PCI DSS. Managed SOC services offer continuous vulnerability management and improvement of security posture to help you meet or exceed the requirements of these regulations.
Low Total Cost of Ownership of Security Technology
Security requires investing in an array of software and tools and operating them in an integrated fashion. Our security operations team has a system of over 30 security tools and applications to secure networks and critical data, saving you the cost and effort. An outsourced model saves you significantly in product license and support costs.
Benefits of Managed SOC Services:
- Continuous insight into the company perimeter is the only way to effectively manage and respond to threats.
- Real-time strategic insight into risk by certified professionals.
- Streamlined processes for continuous monitoring and deeper assessment.
- Preemptively mitigate risk by minimizing vulnerability exploitation time-frames.
Types of Security Assessments
- Security review of organizational security strategy, governance approach, policies, standards, risk management, and staff awareness.
- Technical security review of IT infrastructure, networks, architectures, systems, security procedures, and physical security.
- Combination of both.
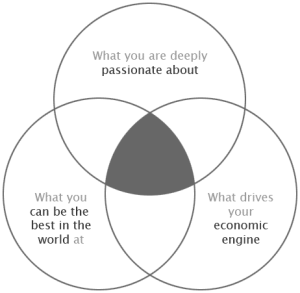
Security Strategy and Roadmap
Once a security assessment has been completed it can form the basis for a security strategy. A security strategy outlines a prioritized plan of action for improving the security posture. Many times we may recommend our managed SIEM services which will help your organization honestly acknowledge the specific risks and challenges and provide a pragmatic approach to managing them. Our systems analysts can focus and coordinate efforts to provide a logical strategic structure that contains three elements: a diagnosis, a guiding policy, and an action plan. This approach is focused on ensuring that you become resilient against an ever-changing threat landscape and that ultimately the organization’s core business operations are protected.
We recommend starting with a cybersecurity framework like NIST that will help you avoid the common mistake of broad ambiguous security goals, ambitions, and vision and instead focus efforts on a set of coherent strategic objectives and implementable actions.
By identifying the state of security, Cybriant will work with you to agree on the right target state to optimize security and develop a prioritized roadmap to achieve it.
PREtect: Cybersecurity Made Easy